Military Electronics: Lessons & Trends
This article succinctly elaborates on prominent areas of military electronics, attracting wide interest globally and in Turkey, from the evolving perspectives of Anti Access/ Area Denial (A2/AD) doctrine, and its interpretations and ramifications. A2/AD Challenges urge us to have a look at all the electronic components of Command, Control, Communications, Computers, Intelligence, Surveillance, Target Acquisition and Reconnaissance (C4ISTAR) to discuss the past experiences, transcend the existing issues, anticipate and comment on the future developments and progress. Turkey has to upgrade its market focus, for the Defense and Aerospace (D&A) industries and products, from only limited to domestic and regional to global markets, to make up for the export revenue gaps and to become a dominant player. The products and ideas mentioned in this article may probably be helpful to realize a path for reaching such a powerful position. In the last section of the article, suggestions have been made for establishing common design/test/reliability methods, architectures, tools, libraries and procedures to reach the goals in a much faster and a more efficient manner.
1-Introduction: Denial Of Access Vs. Safe & Secure Access
The publication of US Department of Defense’s (DoD’s) new strategic guidance and the Joint Operational Access Concept (JOAC), in January 2012, has triggered big debates and discussions on Anti-Access/Area Denial (A2/AD) issues and challenges. DoD’s new strategic guidance mandated JOAC’s implementation as a key component in the U.S. military’s response to A2/AD.
Some of the leading challenges of the future wars will be about establishing and maintaining safe and secure access to physical, spectral and cyber spaces while setting up and sustaining A2/AD to the same spaces by the adversaries. A2/AD is a layered defense approach to slow down, tire out and force the opponent to overspend and waste precious resources in terms of time, lives, ammunition and equipment. It is particularly designed to prevent regional access against a superior enemy that the defender cannot otherwise defeat. However; denying an adversary to have access to a specific area is a natural objective for the incumbent force, and should be considered as an integral component of any military operation.
Strategic land, air, sea and space positions/places may constitute the physical spaces of interest, whereas; electromagnetic spectrum used for surveillance, intelligence collection, navigation and communications today form the spectral spaces. Internet medium constitutes the cyber space and has been and will actively be used in future for preventing and disabling enemy’s cyber capabilities for intelligence gathering, coordination and production of resources (energy, water, waste, etc.), control and manage infrastructure and conducting propaganda as well as misinformation/disinformation attacks.
In future, enemies may lay advanced mines in critical waterways and landing areas, use ultra quiet diesel submarines, or attack offshore staging areas, logistic support points and the space assets with anti-satellite weapons, all in an anti-access effort designed to hamstring the operations and/or make them very difficult and costly. Likewise, A2/AD tactics, such as Radio Frequency (RF) jamming, may impede operations in progress and forces already in the theater. As a result, denial of access presents serious and high priority challenges that must be addressed proactively as well as dynamically.
The current engagement and battle concepts include highly coordinated, cross-domain operations designed to disrupt the adversary’s capabilities for intelligence gathering, surveillance, reconnaissance (ISR) and communications, command, control and computers (C4), which are usually employed for supporting adversary’s:
- A2/AD weapon systems, which may include anti-ship cruise and ballistic missiles, missile-armed combat aircraft, and missile and torpedo-firing submarines,
- Destroy or neutralize friendly A2/AD weapon systems.
Exactly the opposite of “A2/AD” concepts should be defined for setting up and maintaining safe and secure access to physical, spectral and cyber spaces such as “beach-heads”, outposts, strategic points and other important friendly areas, the space as well as the forces in the theatre.
This mainly involves employing the right mix of kinetic weapons applicable to the specific operational situation and requirements. However; the critical role of military electronics need to be factored in achieving control and dominance over all the spaces.
Future of Military Electronics should mostly be considered within the context and considerations of putting A2/AD or “establishing and maintaining safe and secure access” concepts, principles and projections. This can be achieved by projecting the full spectrum objectives over each component of C4ISTAR, and building the required strategies and action plans.
1.1- A2/AD Considerations for Turkey
Turkey is a peace loving and seeking country. It fosters peaceful coexistence rather than survive by creating conflicts and fights. It has been a staunch ally of the West and NATO member since early 1950s. Consequentially, it has taken its place and role in the NATO collective defensive strategies. However; regardless of its affiliation and alliance with NATO, it has to define its own national A2/AD strategies based on its geostrategic position, military heritage, regional balances and recent experiences, as well as its vision as an important energy hub, and an economic and industrial center.
Turkey may supposedly have vulnerabilities coming from the air, seas on three sides, as well as its borders in the east and southeast. It would not be easy to define simple and straightforward A2/AD scenarios and strategies to defend its territory and deter its potential adversaries. Joint strategies have to take into consideration not only the symmetrical wars, but also the asymmetrical battles. The latter has troubled the country for the past 35 years resulting in loss of lives of about forty thousand people. In accordance with these facts and factors, military planners have to find solutions to Turkey’s A2/AD challenges by developing dynamic joint anti-access strategies and capabilities to prevent adversaries from entering strategic points and areas, capturing them and/or causing grave damage. Keeping in mind that A2/AD is a multi-domain and multi-layer joint strategy, its C4ISTAR components and kinetic defensive capabilities in terms of missiles, land/sea mines, quiet conventional submarines and others would all be used to deny a potential opponent having access to air, sea, land, space or cyber domains. Resilience to submarine (SW), electronic (EW) and cyber warfare (CW) has to be improved and/or built. Smart weapons have to be used for improving precision, and thus enabling to conduct warfare from longer distances and minimize collateral damage. C4 and ISTAR capabilities using terrestrial and satellite systems, as well as manned and unmanned airborne platforms have to be beefed up.
2-Electronic And Electromagnetic Warfare (Ew & Emw)(*)
EW and EMW both in how adversaries may have employed and integrated it to their A2/AD strategies, and how friendly forces may have used it, to establish and maintain freedom of movement. Domination of the electromagnetic spectrum is a crucial component of modern military operations and doctrine. This topic is specifically explained and emphasized in “Joint Vision 2020” (JV 2020)(Ref. 12) as an integral part of “Full Spectrum Dominance”. A2/AD defenses can consist of ground based, airborne, naval and space sensors and weapons. Electronic warfare capabilities are needed which can degrade and defeat these defensive capabilities by attacking the system as a whole as well as each individual component, and the Command and Control (C2) links between these components. C2 is heavily reliant on the easy, quick and secure access to electromagnetic spectrum to maximize the efficacy of surveillance, target acquisition and information systems. There will be no air-sea battle without the tools necessary to control the electromagnetic spectrum across land, sea, air, space and cyber domain.
The warfighter needs to be able to control the enemy’s use of the electromagnetic spectrum, ensure friendly access to and use of the electromagnetic spectrum, protect sensors and avionics, maintain secure communications and data links amid electronic and cyber warfare; and maintain navigation, and timing information. It is simply the brave new world of electronic/electromagnetic warfare, where enemies use visible and invisible, and often untraceable, weapons that can theoretically disable everything from satellites and computers to radar and aircraft or destroy them. The goal is to degrade or destroy an adversary’s combat/operational capability, while maintaining the integrity, robustness and security of the friendly combat/operational capability.
For example, North Korea has recently employed portable, truck-mounted, long-range jammers to repeatedly overpower Global Positioning System (GPS) satellite signals in many parts of South Korea. One such attack, in late April and early May 2012, affected the navigation systems of 337 commercial airliners, 122 ships and even cars driving around in metropolitan Seoul. The same vulnerability is applicable to defense systems too. In March 2012, North Korea’s deliberate disruption of GPS signals forced a U.S. reconnaissance aircraft to make an emergency landing.
Similarly, the new generation GPS III satellites, to be launched in 2014, will broadcast using M-code, a much stronger and more secure military signal than P(Y) code. GPS III satellites will improve position, navigation and timing services and provide advanced anti-jamming capabilities yielding superior system security, accuracy and reliability. The first GPS III satellites will deliver signals three times more accurate than current GPS spacecraft and provide three times more power for military users.
Military and defense industry experts/companies have started addressing some of the spectrum related issues, in the recent times. For example, the jamming-resistant Link-16 is being installed on some new unmanned aerial vehicles (UAVs). Link 16 is a TDMA-based secure, jam-resistant digital data/control link, which operates in the frequency band 960–1,215 MHz, and can support throughputs around 250 KBit/s.
Free space optical communications, also known as laser communications, is being developed as an alternate to existing RF control and data links on UAVs, which is much harder to intercept and crack, however more susceptible to rain and snow fading.
Airborne jamming systems can suppress enemy’s air defense radar, and interfere with its communications, data and computer networks, giving friendly forces time and room to maneuver over target territory. One such technology is the Next-Generation Jammer (NGJ), which is being developed for use on airplanes (especially for EA 18G and F-35) and UAVs. NGJ will employ the most up-to-date RF technology, and have a modular and open architecture. The NGJ will have cyber attack capabilities as well. Multiple (most likely 6) broadband electronically steerable antenna arrays will be used, and the system will be fielded by 2020. This means, as a result, that more jamming power will be delivered against multiple targets with more precision.
In future, high power electromagnetic pulses (EMP) can be used as weapons to destroy electronic HW. EMP may occur in the form of a radiated, electric or magnetic field or conducted electrical current depending on the source. They may use the frequency spectral space from DC to daylight. The direct effect of a very large EMP is to induce high currents and voltages in the target, damaging electrical equipment or disrupting its function (very similar to lightning). High power EMPs can be generated by using electric/electronic techniques, usually in directional applications, and by nuclear explosions for wide space coverage. Much of the existing EMP research has involved high power microwaves (HPMs). Potentially, an HPM device could be mounted on a cruise missile, to disrupt ground targets from above. There is credible evidence that such weapons already exist today. Discovering and locating EMP weapons is a new challenge that needs to be addressed in the near future. Much of the work on such weapons is secret, but there are unclassified weapons as well. For example, the US military has funded a Radio Frequency Vehicle Stopper, a satellite dish sized weapon that can be mounted on top of a jeep, which can be used to disable enemy vehicles at a distance.
EMP weapons are likely to find more and more use in future military electronics applications.
(*) Spectrum Warfare (SW) has recently replaced the term Electronic Warfare (EW).
3-Cyberwarfare And Cyber Security
Establishing and preserving cyber security has emerged as the next frontier expanding physical spaces to the ether. The same concepts and principles of A2/AD for adversaries and establishing and sustaining safe and secure access for friendly elements are valid for cyber security as well.
Cyberwarfare refers to politically motivated hacking to conduct sabotage and espionage. Compromising military systems, such as C4ISTAR components, that are responsible for orders and communications, could lead to their interception or malicious replacement. Any number of attacks on government and military departments and defense contractors in different countries, have been widely discussed and covered in the media.
Cyberwarfare has its own offensive weapons. For example, the Stuxnet worm that was discovered in June 2010 and believed to have been created by US and Israel who infiltrated and attacked Iran’s uranium enrichment facilities. In another example, in 1998, US hacked into Serbia’s air defense system to disrupt air traffic control and facilitate the bombing of Serbian targets. As a third example, in 2007, in Estonia, a “Botnet” of over a million zombie computers brought down government, business and media websites across the country. The attack was suspected to have originated in Russia, motivated by political tension between the two countries.
Cyber sabotage targets disruption of services and equipment. Data centers and communication networks including undersea cables, cell networks and satellites that coordinate other activities could be targeted components of a system. Infrastructure components, civil or military, such as power/energy, water, fuel, communications, and transportation all may be obvious cyber sabotage targets and are vulnerable to disruption.
Some noteworthy exploits have resulted in the theft of water (Gignac Canal System in France), the release of raw sewage (Maroochy Shire Sewage plant in Australia), the delivery of incorrect dosages of insulin, printers catching on fire, interference with a Landsat-7 earth observation satellite, and computer viruses infecting the Ground-Control Systems (GCS) of the Predator and Reaper Unmanned Aerial Vehicles (UAVs).
Using cyber weapons is certainly more cost effective and practical than designing, building and testing expensive advanced military weapons and equipment. Cyber domain certainly needs to gain a higher level of consideration, appreciation and priority, when we consider future A2/AD tactics and strategy.
Vigilance in cyber space, similar and analogous to C4ISTAR operations in physical spaces, has to be realized using cyber techniques and tools such as DPI, LI, data/information storage, mining, analysis and fusion.
4-Challenges In Satellite Technology
Satellite systems offer and provide warfighters with some important C4ISTAR details, namely ISR information, strategic defense warning, precision positioning, guidance, navigation, timing and stationary and on-the-go communication capabilities that are essential components of imposing A2/DA conditions. Threats to space systems and assets used to be treated as tolerable risks, considering that an attack in space might be provocative, encouraging retaliation, and in consequence, might easily trigger escalation. It might also be accepted as an open invitation to a nuclear war. However; significant changes have taken place in security and defensive concepts and approaches for space, in terms of spreading the asset base, building more redundancy and networking them together, to lessen the impact of any partial damage to the system and improve survivability of the function.
January 11, 2007, the People’s Republic of China successfully destroyed a defunct Chinese weather satellite, FY-1C. This has been an “eye-opener” and exposed the vulnerability of space assets. Since then dependency on GPS system for guidance and navigation of all the smart weapons has totally changed. Although GPS III satellites, operating with more secure M-code, will be launched next year, global secure navigation, from now on, may rather rely on Inertial Navigation System (INS) and Terrain Referenced Navigation (TRN), together with Altitude and Heading Referenced System (AHRS).
Big and sophisticated satellites, with many sensors and processing capability have been primary space targets, are no longer needed. Space assets lie on many much smaller satellites with specific functions onboard, so that it is too difficult to destroy all of them at once. TR may have to adopt a similar approach and avoid putting all communications and observation capabilities in medium to large satellites as Göktürk-1, 2 & 3.
A current challenge may be mentioned as networking all the small and widely distributed space assets by using self-forming, self-healing, multi-hop mesh network technology, in which every node has self-beaconing and repeater capability. Data communications with Earth is established at one or more nodes at which the mesh network protocol operates over a Demand/Permanently Assigned Multiple Access (DAMA/PAMA) protocol.
5-Remotely Controlled And Operated Vehicles (RCOVS)
Use of RCOVs, for both military and civil applications, has currently been going through an explosive growth in the forms of Unmanned Aerial Vehicles (UAVs), Unmanned Combat Aerial Vehicles (UCAVs), Unmanned Ground Vehicles (UGVs), Unmanned Underwater Vehicles (UUVs) and robots. RCOVs are being used for C4ISTAR operations and in combat roles against civilian and strategic targets. Robust and secure command and control (C2), as well as guidance and navigation of RCOVs, under harsh and EW conditions, has to be maintained. Data from multiple on-board sensors have to be collected, processed, fused together, and relayed to the ground stations securely.
The capture of the most sophisticated and stealth US drone, by the Iranians, presents a good case and lesson that needs to be analyzed and learned from about how an UAV can be attacked, hijacked and captured with minimal damages by the adversaries, and what precautions and solutions can be developed against these attacks by next generation military electronics.
“On 4 December 2011, an American Lockheed Martin RQ-170 Sentinel Unmanned Aerial Vehicle (UAV) was captured by Iranian forces near the city of Kashmar in northeastern Iran. The Iranian government announced that the UAV, operated by the Central Intelligence Agency (CIA), was brought down by its cyber-warfare unit, that commandeered the aircraft and safely landed it. It was explained later that, the drone was captured by jamming both satellite and land-originated control signals to the UAV, followed up by a GPS spoofing attack that fed the UAV false GPS data to make it land in Iran at what the drone thought was its home base in Afghanistan. An expert from Flight Global assumes UAV guidance could be targeted by 1L222 Avtobaza radar jamming and deception system supplied to Iran by Russia.”
UAV system developers strive to enhance UAVs with ever more autonomy, collision avoidance, more powerful sensors, better data fusion from multiple sensors, and more robust, secure and fatter data and control links. Low level routine pilot/operator tasks and duties, such as cruise control (speed and altitude), flight path surveillance and flight pattern maintenance functions have been built-in on more developed UAVs. For further progress and integration of UAVs into the national air spaces “coexistence”, “right-of-way”, “see-and avoid” and/or “sense-and-avoid” rules and regulations have to be defined and implemented. This may necessitate better localization of the UAVs by on-board and off-board (both air and/or ground) sensors. Active/passive noise cancellations techniques have to be implemented to make UAVs more silent, and therefore; more eco-friendly as well as more undetectable.
For military purposes, “latency in data processing, and command, control and communications (C3)” is a critical parameter, for collecting the sensor data, fusing them together, communicating the findings and taking consequential action. More than few seconds delay in this process may be long enough to determine success or failure of the operation. Measures and countermeasures for anti-UAV systems and weapons, for single and swarm of UAVs, need to be developed, as well. EMP and high power shotgun like weapons could be considered for anti-UAV applications. In April 2013 a laser weapon prototype was announced and deployed in the Persian Gulf. For the first time the ships are going to be equipped with a laser attack weapon able to disable patrol boats, and blind, or destroy surveillance UAVs, as the tests have shown. This new capability is referred to as “Laser Weapon System (LAWS)”.
As the unmanned air vehicles are becoming more and more ubiquitous, the improved systems and mission capability of UAVs/UCAVs will cause larger investments in simulators to train pilots/operators. Currently, a bigger number of unmanned aerial systems pilots than all the others are being trained based on expanding roles for and increasing dependence on the UAV/UCAV capabilities. This enhanced demand and reliance on UAVs will need and bring improved simulation reality, fidelity and integration with live platforms, for effective, efficient and economical use of resources. This will require improvements in the quality of the simulations especially considering the effects of environmental factors like topography, climate and the presence and actions of other elements like air traffic and missiles or facilities, weapons and enemy actions on the ground. These should be unscripted and indistinguishable from the real life. For an increased reliance on simulators and to speed up the certification process of new pilots, the need for institutionalizing a formal training plan and program for unmanned systems operators should be emphasized.
6-Video Signal Processing
UAVs and UCAVs may carry multiples of sensors for different portions of the visible and invisible light spectrum including UV and IR. Therefore; lossless and reliable video signal processing, compression and fusion are necessary due to the limited available bandwidth over the secure data links from UAVs to the Ground Control Stations (GCS).
There is significant in-house experience and expertise for fracturing digitized and compressed (H.264) video information into several digital streams, applying Forward Error Correction (FEC), sending them over different communication channels with different characteristics and anomalies, and realigning the video and audio signals, and bonding them together at the receive end to form a single video stream. A portable commercial product, MODEO, is currently on the market being targeted for live TV broadcast, boarder surveillance and control and security applications. This expertise makes it possible to integrate video signal processing and secure data link technologies together on different civil and military platforms, including UAVs, as a use and application of future military electronics technology.
7-Ultrawideband (Uwb) And Cognitive Radio (Cr) Technologies
UWB and CR have been two recently investigated and employed spectrum re-use technologies, that can coexist with the incumbent spectrum users, for gaining easy and complementary access to electromagnetic spectrum, and can potentially find more applications in future for civil and military applications.
UWB technology is used for transmission of multimedia signals below the background noise levels, and has been used for implementing covert radios, that can only be detected by special wideband receivers. UWB signal spectrum covers at least a continuous band of 500 MHz by definition. Higher power UWB radios can be noticed as “noise floor raise” by narrowband radio receivers. Due to its wide bandwidth, it has the indigenous capability to carry and support high data rates over short ranges. It is commonly used in sensor networking applications. UWB technology is also used in civil, military and security applications for imaging through the objects such as, through the wall imaging to see what’s beyond the walls in hazardous situations, ground penetrating radar and suicide bomber detection.
Electromagnetic spectrum has been over allocated. Some frequency bands have been allocated multiple times for primary use. Cognitive Radio (CR) technology takes advantage of unused electromagnetic spectrum geographically and on time basis, in an opportunistic and dynamic manner as a secondary user. A CR is a smart system and aware of the spectral rules and regulations for the intended frequency bands (in terms of allowable transmit power, channelization, propagation template, etc.), as well as the usage times of the primary and secondary owners of the spectrum. A CR has location and spectrum sensing capability to detect the presence of active transmitters, as well as a database to have a priori knowledge of the operation times and the edges of the propagation contours of the incumbent radios. If “Allowable Noise Temperature” is known for a location, a CR has the ability to adjust its transmit power level not to exceed this limit. A CR network deploys itself at a selected frequency while keeping track of a list of all the other available frequencies that it can use. This list is shared with all the members of the network, and in case a spectrum usage conflict arises, the whole network jumps, at once and in coordination, to the next available frequency on the shared list, without any interruption in the service, even if a guaranteed QoS may exist.
Frequency agility and dynamic spectrum access capabilities of a CR system, running on a Software Defined Radio (SDR) platform, provides itself with an inherent resistance to EW. When used together with spread spectrum techniques (especially FHSS), the immunity level gets boosted significantly. This makes CR technology a very good candidate for tactical networking and communications applications on the battlefield. CR technology has been used in spectrally congested environments and times to guarantee access to the networks, such as by smart phones in crowded urban areas, as well as hazard and/or emergency conditions.
Taking the ever increasing congestion on the frequency spectrum and the exponential rise in the number of wireless applications and users into consideration, both UWB and CR have the potential to find myriad of uses in future military electronics applications, potentially many of them on the battlefield.
8-Passive Radars (Prs)
With the proliferation of the stealth technology, anti-stealth options and remedies have been under intense focus. One such solution, Passive Radar (PR), has been discussed extensively in the recent times for their ability to detect stealth aircraft.
Active radars have been designed and used for providing surveillance information and identifying targets. However, they emit powerful EM waves, and therefore, can easily be detected, jammed and destroyed. Stealth planes are usually flown over the target territory, preceding military operations, to discover and destroy surveillance radars and weapons using active radars. Therefore, detecting, tracking and shooting down stealth aircraft are essentially required for achieving A2/AD conditions over adversary forces. Since they do not emit any electromagnetic energy and use an integrated system of netted receivers, passive radars operate covertly, and stealth aircraft have no means of detecting them. They can be well camouflaged, and/or placed on mobile platforms, and distributed over rural landscapes.
Stealth technology is based on minimizing the reflective profile of a flying object. Emitted radar signals are reflected back from the objects revealing their position and other flight characteristics. Stealth platforms usually have wide and shallow edges and some perpendicular surfaces to absorb and reflect away radar signals to avoid detection. An object may be invisible at some wavelengths and some angles of approach, however; it cannot be completely unseen and undetectable over a wide range of frequencies as well as angles of incidence.
There is no dedicated transmitter in a passive radar system, and as a result they have excellent Low Probability of Interception (LPI) properties. The receiver uses third-party transmitters (Transmitters of Opportunity (ToO)) that are constantly present around us, and operate over a wide spectrum, such as TV and/or FM radio stations and/or cell phone networks. A PR receiver measures the time difference of arrival between the signal coming directly from a known transmitter and the signal reflected from the object of interest. This makes measuring of the bi-static range of the object possible. Besides the bi-static range, a PR is also able to measure the bi-static Doppler shift of the echo as well as its direction of arrival. With these measurements, the location, heading, speed acceleration and the flight path of the object can be calculated. It may also be possible to estimate the size of the flying object. Triangulating signals from several different sources can help build up a picture of a landscape or sea surface or airspace, thus making stealth planes and stealth ships as visible as others.
Deploying PR systems and providing wide territorial coverage is key for establishing A2/AD conditions and preventing stealth attacks over designated areas.
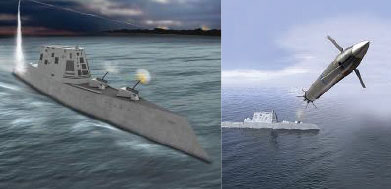
9-Smart Weapons/Precision Guided Munitions (Pgms)
With the development of advanced electronic sensor and guidance systems, improved jet and rocket propulsion, and micro-machining, weapons designers have been able to improve on bomb technology to build “smart” bombs and missiles that can perform precision attacks on targets. Smart weapons will be particularly relevant, effective and strategic as wider areas of land, sea and air get designated as A2/AD zones, and as the related mission challenges are tackled.
The impact and damage effects of explosive weapons decrease with the cube of the distance from the aim point. As an example, if the hit point is 10 meters away from the target, then the damage would be reduced by around 1000 times. To be classified as a Precision Weapon (PW), it has to have Circular Error Probability (CEP) accuracy of 3 meters or less. The improved accuracy of PGMs allows us to reduce the harm to civilians and the amount of collateral damage, and put less crew lives at risk. PGMs will also allow us employ and utilize smart and decisive fighting power at further distances.
At the outset of the Vietnam War, Thanh Hoa Bridge (The Dragon’s Jaw Bridge) spanning the Song Ma River, situated 110 km south of Hanoi, was rated as No. 14 on the list of the most important targets in North Vietnam. It carried the only railroad in the North Vietnamese panhandle and was a key link in the supply route supporting the war in the south. Starting in 1965, 871 sorties were made and 11 planes lost without managing to make it unusable. In 1972 the “Dragon’s Jaw” bridge was attacked with Laser Guided Bombs (LGBs) and 14 jets succeeded, in a single operation, dropped the span, and cut a critical supply artery.
Early PGMs were built by retrofitting gravity bombs with laser guidance packages resulting in Laser Guided Bombs (LGBs). LGBs and IR guided weapons are susceptible to poor visibility conditions. After the advent of GPS, Joint Direct Attack Munition (JDAM) was introduced, which quickly became the smart bomb of choice. However, GPS signals can be jammed, and may not be reliable over a certain area. If the targeting information is accurate, and if there is no GPS jamming, satellite-guided weapons have a higher probability of achieving a successful strike under all-weather conditions than any other type of PGM. In some hybrid systems, the guidance is reverted to inertial navigation when GPS signal is lost or compromised. Since CEP radius of INS (30m) is much bigger than GPS (13m) for long glide times (about 100s), Terrain Referenced Navigation (TRN) system, together with Attitude and Heading Referenced System (AHRS), complement most up-to-date hybrid navigation packages. Thus shortcomings emerging from bad weather and other adverse conditions can be overcome by enabling different options present in the hybrid packages.
Turkey has developed its own advanced JDAM adaptation kit with improved characteristics over competition. TUBITAK-SAGE’s HGK (Hassas Güdüm Kiti) is a state of the art GPS/INS guidance kit that turns existing 2000 lb MK-84 dumb bomb into a smart weapon. TUBITAK-SAGE has also designed and built two Smart Wing Adapter Kits (KGKs) for precision guidance adaptation of MK-82 500 lb and MK-83 1000 lb low-drag, gravity bombs.
Cannon Launched Guided Projectiles (CLGPs) are PGMs that are fired from conventional artillery and/or cannons on warships and armored vehicles. The electronic modules/units in a missile warhead are subjected to a few times the normal gravitational force, whereas a gun-fired munition may experience more than 20,000 Gs. Also considering the extreme pressures of around 5 tons per square cm in a 155 mm gun, the engineers must overcome extreme conditions and constraints when designing such projectiles as the Extended Range Guided Munition (ERGM). Using the most advanced GPS/IMU technology, ERGM is intended for hitting targets as distant as 50 kilometers, with a Circle of Equal Probability (CEP) accuracy of 20 meters. There also exists a precision guidance kit to refit existing 155mm shells with precision guidance (XM1156), as the JDAM kit converts dumb bombs into precision munitions.
Precision-guided small arms prototypes have been developed which use a laser designator to guide an electronically actuated bullet to a target. Micro sensors have been under development to be crucial parts of advanced Inertial Measurement Units (IMUs), and small enough for guided munitions, hand-held devices, and add-in portable guidance, navigation, and control units. There are projects, underway with some early demonstrations for developing MEMS based Microscale Rate Integrating Gyroscope (MRIG), for guided munitions and hand-held devices.
10-Battlefield (Tactical) Networking And Communications
Improved Battlefield Networking and Communications (BN&C) aims to make significant enhancements to the connectivity and communication capabilities of the warfighter by providing more, better, trusted and tailored information for situational awareness, including C4ISTAR details. The guiding principles of BN&C have been described in JV 2020, WHİCH states the current doctrines and approaches to establish “Full Spectrum Dominance” (FSD) that covers a wide range of operations from humanitarian assistance, to civil support, to peace keeping/enforcement, to counter terrorism, to conventional warfighting. The communications for the last one is the main topic of this section. A key component of FSD is “Information Dominance” reached through “Superior Information” which is converted to “Superior Knowledge”, and finally, superior knowledge is essential for obtaining “Decision Superiority”.
In pursuit of obtaining decision superiority, conflicts will mainly be about acquiring, processing and communicating knowledge. In a distributed non-hierarchical network (i.e. the Digitized Battlefield Network), Command and Control (C2) messages and information flow do not necessarily follow the same routes, contrary to the flows in hierarchical networks. A network grid connects sensors, weapon systems and commanders so that, the situational awareness data can be shared by all units, while C2 is directed and coordinated according to the order of battle. To set up a Global Information Grid (GIG) for achieving information superiority, the reference model and the system architecture have been adopted from the private sector rather than the extensions of legacy military communications models and architectures that are based on circuit-switched principles. Capabilities offered by a modern IP based GIG can enable a commander to stand on a, local or remote, “electronic hilltop” to monitor and conduct the action on the battlefield.
The shift in focus, from “platform” to “network”, and progress in public wireless networks have led to the emergence of the “Network Centric Warfare” (NCW) concept. The information network, that supports NCW, has to provide broadband integrated multimedia services and be easily deployable, self organizing, high speed, scalable, flexible (bandwidth on demand), easy to join/leave (if authenticated and authorized), dynamically reconfigurable, real-time, robust, secure, self-forming/healing and EW resistant.
Integrated information systems on the battlefield cannot be supported by legacy military networks, which were mainly designed and built for carrying digitized voice and narrowband data. However; modern tactical information and communication systems, supporting NCW, have to enable warfighters for taking commands horizontally and vertically, collecting, synchronizing and fusing real-time strategic, tactical and joint information to quickly analyze results, make decisions, and take action accordingly. To achieve this, High Definition (HD) Audio and Video (A/V) teleconferencing, Electronic Messaging (EM), sensor data and inter-networked data services have to be shared and supported by battlefield networks. This creates a big demand for large volumes of data for the warfighters, and as a consequence, fat, robust and secure pipes of transmission as well as efficient networking protocols and routing capabilities are needed for enhancing coordination and improving the efficacy of battlefield operations.
Tactical IP based communications, connecting TCP/IP host computers, other IP data networks and having remote access to the Tactical Internet, over wideband radios using commercial routers and customized lower layer protocols to packetize a traditionally voice oriented signals, have been instrumental in the development of the early versions of the modern battlefield communications. Today, multiple high speed ground and airborne routers and gateways, network servers and wideband radios that can provide Beyond Line of Sight (BLOS) connections, constitute the essential components and enablers of the modern battlefield networks and communications. These gateways can translate and map, encapsulate and distribute IP based voice, video, imagery and other pertinent battle-space information coming from various sensors, including radars.
The Battlefield Airborne Communications Node (BACN) and its ground counterpart Rapid Attack Information Dissemination Execution Relay (RAIDER) are the gateways defined and developed for BN&C applications. BACs are carried on manned/unmanned airborne platforms. A Common Data Link (CDL) connects the BACN to the ground gateway/terminal at a Prime Node. BACN and , similar to their equivalents in public networks, are the key elements of the battlefield networks, and perform all the router functions (PHY, Data Link & Networking Layers) plus Transport and Session Layer functions, of ISO’s Open System Interconnection (OSI) model, to do protocol translation and mapping. There are two possible implementations of the networking on the battlefield. The first one is straight forward, in which a mobile cellular base station establishes the connections to the smart phone or tablet like terminals on warfighters. The second one is more elegant, cutting edge but more challenging as well. It comes in the form of a Mobile Ad Hoc Network (MANET) that is based on wireless mesh networking technology, and has the ability to implement all the previously mentioned static and dynamic attributes of BN&C. It can inherently provide scalable high bandwidth networking capabilities, using RSVP protocol, for a limited group of handheld terminal devices, terminals on ground/air vehicles, and security and tactical sensors. Each node of the network has equal privileges with repeater and routing capability, and QoS can be supported for a limited number of hops in the mesh.
The interoperability and security concerns still linger around, especially for the IP based networks, and have to be overcome for the mass deployment and widespread use of smart phone and tablet like devices on the battlefield. In the complete network picture (Please see Fig. 6), SATCOM links are used as backups and bridges to other networks and Internet, since there exist limitations generally imposed by latency as well as practicality.
11-Defense And Aerospace (D&A) Industry Eco-System, Common Design/Test/Reliability Methods, Tools And Procedures
Turkey’s recent growth economically and influentially, has made it a regional and global role model. D&A industry revenues and exports have grown proportionally. D&A exports are expected to reach USD 1.7B this year, and the export target for year 2016 is USD 2B (Please see Ref. 18). This urges Turkish D&A industry to compete for larger scale international projects in the global markets, including the developed countries, to make up for the revenue gap. While raising the bar for the export revenues, industrial efforts should be organized and supported by establishing an eco-system and encouraging development of new technologies and products, like the ones mentioned above in the previous sections of this article.
An eco-system contains all the necessary industrial, commercial, regulatory functions, test and certification labs as well as some financial services for encouraging and stimulating entrepreneurship. A good example of an eco-system may already exist in Turkey for the auto manufacturing industry with all the supporting functions. However, a locally designed and produced national car is yet to appear, because of severe competition in auto industry and market conditions. An eco-system for D&A industry may partially exist in the form of defense electronics companies and SMEs. However; completing the system would be more difficult due to much tougher and more complicated operational conditions, standards and related requirements. Lack of expertise and competent brainpower, in many different disciplines, delay the process and make it even harder to build the D&A industry eco-system.
In the past 20 years military system planners have heavily relied on Commercially Off-The-Shelf (COTS) technologies and products. Throughout this period, embedded computing standards were closely adhered to in terms of chassis, boards backplanes and electrical interfaces, and costs were of secondary concerns. Today, however; with ever tightening military technology budgets, the trend is turning towards using more open source solutions, emphasizing and putting the priority on functionality and cost. The application itself is the starting point and the main driver of the process for devising a solution. The system designers then search for the optimum preconfigured embedded platform that can adequately run the application. They consider/reconsider all available ready-to-run platform products that can do the job, and are cheaper than the established standards based solutions, such as VME, VXS, VPX and even Open VPX. Micro Telecommunications Computing Architecture (Micro TCA) is a standard for open modular systems and is much cheaper than the others, and therefore has recently been a highly considered choice. It has enough bandwidth for most challenging applications, and is especially designed for applications requiring high communication bandwidth, high processing power and high availability. Cost pressures and the consequential choice for ready-to-go platform solutions have led to the adoption of “Low Price, Technically Acceptable (LPTA)” approach for the technology purchases. This new philosophy has rightfully raised concerns about the risk of adversaries obtaining the same or similar technologies, especially in the HW. With open source common products, the difference would be in the FW/SW coding, noting that there is always a probability of getting some malicious codes. However; this probability has been minimized and is almost zero due to peer reviews and procedural checks.
To jump-start and speed up development of new products, with functionality and cost in mind, the efforts have to be organized around defining and selecting common development methods, processes, functional architectures, interfaces, HW/SW/FW libraries, tools and platforms for design, test, manufacturing, reliability and interoperability purposes and for easy implementation and faster transitioning into future military electronic systems. Traditionally and even before COTS times, adhering to rigid military standards, and letting the companies use their own internal processes, methods and design/test/qualification environment had been the main policy. However; streamlining the design, development and productization processes in an eco-system, by using common and preferred means, tools, architectures and approaches, the expertise base can potentially be widened into many different defense companies, product design and manufacturing cycles may be shortened, interoperability may be established more easily and R&D costs may be lowered considerably.
It is respectfully suggested (without any negative connotation) here that Undersecretariat for Defense Industries (SSM) would be the natural leaders to direct the efforts, for defining and coordinating these activities. Determining alternatives and selecting common and/or preferred design, test and manufacturing methodologies and environment for HW and SW is first part of the story and may contain:
Integrated design procedures with built in design reviews at every stage;
System simulations and verification with behavioral models,
Use of Design for Test (DFT) principles from the start,
Integrated circuit analysis, synthesis, simulation and verification environment and tools for analog, digital and RF circuits (whichever applicable).
Electrical and environmental testing and qualification:
Reconfigurable analog and digital automatic test systems,
Reliability testing and product qualification, which may include:
Life testing
Temperature cycling
Humidity testing
Drop testing
Pull testing
EMI/EMC testing
Others
These tests may be performed at qualified and approved test laboratories:
Conformance to standards,
Compatibility and interoperability testing
The second part of the story is about using common and preferred tools components, modules, sub-systems, systems and SW modules to quicken the design and manufacturing process as well as guaranteeing some specs and conformance by design:
Micro controller (uC) boards,
Digital Signal Processor (DSP) boards,
D/A and A/D chips and boards,
FPGA chips and design systems,
Soft and hard analog and digital libraries,
Communication protocol design platforms,
XOs, TCXOs, VCOs, VCXOs, Frequency synthesizers
Up/down converters, IF/RF modules,
Filters, baluns and RF switches,
Antennas,
LNAs and Pas,
As concluding remarks on this section, the conditions and advantages offered by the financial crisis in the western world have to be recognized, to take advantage of the “once-in-a-several-hundred years opportunity”, and actions have to be taken for jump-starting R&D and innovation efforts:
Bringing leading scientists and engineers for target military electronics projects,
Acquire abroad some target innovation companies,
Invest abroad in some other target innovation companies,
Set up partnerships with and/or give lucrative incentives to established foreign military companies to do their R&D works locally in Turkey.
12-Conclusions
Future of Military Electronics needs to be looked at from the viewpoint of Anti Access/Denial Area concepts and principles, and A2/AD Challenges urges us to have a look at all the electronic components of C4ISTAR to discuss the past experiences, transcend the existing issues, anticipate the future needs and comment on its evolution and progress.
In future, there will be no air-sea battle without the tools necessary to control and dominate electromagnetic spectrum across land, sea, air, space and cyber domain.
Cyber domain certainly needs to gain a higher level of consideration, appreciation and priority, when we consider future A2/AD scenarios tactics and strategy. Using cyber weapons is certainly more cost effective and practical than designing, building and testing expensive advanced military weapons and equipment.
EMP weapons are considered one of the most dangerous threats facing modern electric and electronic systems and infrastructure, with its ability to induce mis/dysfunction or damage electronic devices. Man made EMP weapons can be used to deliberately disable power grids and defense and security systems without leaving any trace as to the specific nature or origin of the weapon. Discovering and locating EMP weapons is a new challenge that needs to be addressed in the near future.
- Big and sophisticated satellites, with many sensors and information processing capability have been primary space targets. Today, space assets have been spread on many much smaller satellites with specific functions, so that it is too difficult to destroy all of them at once. A current challenge may is to network all the small and widely distributed space assets by using self-forming, self-healing, multi-hop mesh network technology.
RCOVs are being used for C4ISTAR operations and in combat roles against civilian and strategic targets. Robust and secure command and control (C2), as well as guidance and navigation of RCOVs, under harsh and EW conditions, has to be established and maintained.
The enhanced demand and reliance on UAVs will need and bring improved simulation reality, fidelity and integration with live platforms, for effective, efficient and economical use of resources.
There is limited bandwidth available on LOS and BLOS secure data links, urging us to implement lossless and reliable video signal processing, compression and fusion onboard the UAVs/UCAVs.
CR and UWB are spectrum reuse technologies. Taking the ever increasing congestion on the frequency spectrum and the exponential rise in the number of wireless applications and users into consideration, both UWB and CR have the potential to find myriad of uses in future military electronics applications.
Passive radar is used for detecting, tracking and shooting down stealth aircraft, which is essentially required for establishing and forcing A2/AD conditions over adversary forces.
Smart weapons will be particularly relevant, effective and strategic as increased sea and land areas get designated as A2/AD zones, and as the associated mission challenges are tackled. PGMs will allow us employ and utilize smart and decisive fighting power from longer distances with minimum amount of collateral damage.
High Definition (HD) Audio and Video (A/V) teleconferencing, Electronic Messaging (EM), sensor data and inter-networked data services have to be shared and supported by battlefield networks. This creates a big demand for large volumes of data for the warfighters, and as a consequence, fat, robust and secure pipes of transmission as well as efficient networking protocols and routing capabilities are needed for enhancing coordination an improving the efficacy of battlefield operations.
The expertise base for Defense and Aerospace (D&A) industry can potentially be widened into many different companies, product design and manufacturing cycles may be shortened, interoperability may be established more easily and R&D costs may be lowered considerably by using common and preferred procedures, tools, architectures, approaches and testing. This would ensure faster transitioning into future military electronic systems.
C2Tech has different and significant expertise areas in secure satellite communications, cyber security and defense, secure LOS and BLOS control and data links for airborne platforms, video signal processing and streaming, software defined radar and defense simulations to help shaping the future of military electronics efforts in Turkey.